Just-in-time access: how to eliminate standing privileges and reduce risk
Just-in-time access eliminates standing privileges by granting temporary, time-bound permissions on demand. Learn how JIT access supports zero trust and reduces identity risk.

Featured event: A CISO’s take
Join Jim Alkove and Ramy Houssaini to learn how forward-thinking security teams are addressing Enterprise AI Copilot risks.
Most users in your enterprise hold access they haven't touched in weeks. Some haven't used it in months. That access remains persistent and live, ready for whoever gets to it first: your employee — or an attacker with compromised credentials.
That's the standing privilege problem. And it's not an edge case. It's the default state of most enterprise identity environments.
Just-in-time access (JIT access) is the operational shift away from that model. Instead of always-on access, JIT access is granted when needed, scoped to the task, and automatically removed when the window closes. JIT access is a core zero trust principle.
This article breaks down what just-in-time access is, how it works in practice, where it applies across your environment, and how to implement it without turning your approval queue into a bottleneck.
What is just-in-time access?
JIT access definition
Just-in-time access is a security model where permissions are granted dynamically, bounded by time, and scoped to a specific task or session. When the work is done or the time window expires, access is automatically revoked.
The acronym JIT comes from manufacturing (just-in-time inventory), and the principle maps cleanly: you get what you need, when you need it, in exactly the quantity required.
In identity security terms, JIT means a user submits a request, a policy engine evaluates it, access is provisioned for a defined window, and revocation is automatic. The access lifecycle is explicit, bounded, and auditable.
What are standing privileges?
Standing privileges are the opposite: persistent access rights that users hold regardless of whether they're actively using them. A sysadmin who has had domain admin rights for three years — whether or not they use them daily — holds standing privileges. So does the contractor whose VPN credentials technically expired six months ago but were never revoked.
Most enterprise environments are built on standing privileges by default. Access is provisioned at onboarding, modified occasionally when someone changes roles, and often never reviewed until something goes wrong. Verizon's 2025 Data Breach Investigations Report found that credential abuse is the leading initial attack vector, and most of those credentials carried far more access than the attacker needed to do damage. Standing privileges are the reason the blast radius is so large.
Where JIT access fits in zero trust
Zero trust's foundational principle — never trust, always verify — is well understood in network security. Least privilege is one of the essential concepts within zero trust. Like zero trust, least privilege as a concept is easy to agree with — but enforcing it continuously across thousands of users, roles, and systems without daily friction is the hard part.
JIT access makes least privilege practical at scale by shifting access from a static configuration to a dynamic, policy-driven workflow. You're not trying to maintain the perfect permission set for every user at all times. You're granting specific access for specific reasons, then letting it expire.
JIT access vs. standing privileges
The risk of always-on access
Standing privileges are a primary attack surface for three interconnected reasons.
- Dormant accounts: Users accumulate access over time. A developer who rotated through a project team two years ago may still hold production database access. That account sits idle — until it's compromised.
- Lateral movement: Once an attacker has valid credentials, standing privileges determine how far they can move. Broader access means broader damage. IBM's 2025 Cost of a Data Breach Report put the average breach cost at $4.4 million, and privilege escalation is consistently one of the key vectors that drives that number up.
- Over-permissioned roles: Role bloat is real. When access is easier to add than to remove, roles accumulate permissions over time. Periodic reviews catch some of it, but most stays.
How JIT access changes the security equation
JIT access compresses the exposure window. Here’s the workflow:
- a user or system submits a request
- a policy engine evaluates it against role, risk level, and context
- access is provisioned for a defined window (two hours, one day, a specific session)
- at expiration or task completion, access is automatically revoked
The attacker who compromises a credential between requests gets nothing. The dormant account problem largely disappears because accounts don't hold persistent access. Lateral movement is constrained to whatever was explicitly granted, for however long the window was open.
JIT access and the principle of least privilege
Least privilege has two dimensions: scope and time. Most implementations focus on scope, making sure users only have access to the systems and data their role requires. JIT adds the time dimension, so scoping goes beyond what access is granted to consider when it's valid.
That's the difference between "this user has read access to this database" and "this user has read access to this database for the next four hours because they're running a specific audit." Both are least privilege, but only one expires.
How just-in-time access works
The JIT access request workflow
A well-designed JIT workflow has five stages:
- Request: A user or automated system submits an access request specifying the resource, the reason, and the required duration.
- Policy evaluation: The policy engine checks the request against predefined rules: the user's role, the sensitivity of the resource, time of day, location, and recent activity patterns.
- Approval: Depending on risk level, the request is either auto-approved or routed for human review.
- Provisioning: Time-bound access is granted. The user gets exactly what they asked for, with a defined expiration.
- Revocation: At expiration or task completion, access is automatically removed. The full transaction is logged.
The key design principle: revocation is never manual. The moment revocation depends on a human remembering to act, you've reintroduced the standing privilege problem.
Approval models: automated vs. human-in-the-loop
Not every JIT request warrants a human reviewer. A developer requesting read access to a non-production environment during business hours doesn't need an approval ticket. A contractor requesting admin access to a production database at 11 PM on a Friday does.
Auto-approval makes sense for low-risk, routine requests where the policy context is well understood: the user has an established pattern, the resource sensitivity is low, and the request fits normal parameters.
Human-in-the-loop approval is warranted for privileged systems, sensitive data stores, unusual request patterns, or any context where the policy engine can't confidently assess risk. The goal is to route the right requests to humans — not every request.
Session-based vs. role-based JIT
Session-based JIT grants access for a single session or task. The permission is tied to the session token, so when the session ends, so does the access. This works well for database access, remote administration, and break-glass scenarios.
Role-based JIT temporarily elevates a user into a higher-privilege role. Rather than permanently assign the user to the role, they're elevated for a defined window, then dropped back to their baseline. This model works well in environments with established role hierarchies where role elevation is the natural request pattern.
Neither model is inherently better. The right choice depends on your identity architecture and the systems you're governing.
JIT access for non-human identities
Service accounts, bots, CI/CD pipelines, and API tokens are not exempt from the standing privilege problem. In many environments, they're worse than human accounts: highly privileged, rarely reviewed, and almost never deprovisioned on a meaningful schedule.
JIT principles apply to non-human identities (NHIs), too. A service account that only needs database credentials during a nightly batch job doesn't need persistent database access. An API token scoped to a specific pipeline run doesn't need to live indefinitely. Governing NHIs with the same time-bound, purpose-scoped access model as human users closes one of the most consistently overlooked attack surfaces in enterprise environments.
Just-in-time access use cases
Privileged access for IT and security teams
This is the classic JIT use case. Sysadmins, security engineers, and IT operations staff often need root or admin-level access — but not continuously. A sysadmin might need elevated access twice a week for specific maintenance tasks. There's no security justification for maintaining 24/7 access.
JIT replaces permanent privileged accounts with on-demand elevation. The admin requests access, gets it for the task window, and returns to a baseline role when the window closes. Privileged access management (PAM) tools have historically addressed this space, and JIT is increasingly the architectural principle behind modern PAM.
Contractor and third-party access
Vendors and contractors represent one of the highest-risk standing privilege scenarios in the enterprise. Access is provisioned at the start of an engagement, often broadly scoped, and rarely removed when the engagement ends.
JIT solves this structurally. Access is scoped to the engagement window from the start, with a defined expiration that matches the contract term. If the engagement extends, the access window extends with a fresh approval. If it ends early, access expires on schedule regardless of whether someone remembers to offboard the vendor.
Emergency access ("break glass")
When something goes wrong at 2 AM, teams need elevated access fast. The traditional solution is a shared break-glass account, which is a privileged credential reserved for emergencies that is therefore permanently exposed.
JIT break-glass workflows enable emergency elevation without permanent backdoors. A user requests break-glass access, the request is auto-approved with an elevated logging profile, access is granted for a short emergency window, and every action taken during that window is fully audited. The access is traceable to a specific person, a specific reason, and a specific time window.
Compliance-driven access windows
In regulated environments — such as SOX, HIPAA, and PCI DSS — auditability is non-negotiable. Auditors want to know who had access to what, when, and why. Standing privileges make that question hard to answer. JIT makes it trivial. Every grant is logged, time-stamped, and tied to a business justification. The audit trail is a natural byproduct of the access model, not a separate compliance exercise.
Implementing just-in-time access policies
Define what requires JIT vs. standard access
JIT is not a universal answer for every access decision in your environment. Start with the highest-risk areas: privileged systems, production data stores, sensitive customer data, and critical infrastructure. Map your current standing privilege landscape first — who holds persistent privileged access, and how often is it actually used? Accounts with broad access but low or no activity are your first priority.
Build approval workflows that don't slow teams down
JIT fails operationally if the approval process takes 45 minutes. If engineers start looking for workarounds because the access request process is slower than the work itself, you've solved a security problem by creating a new one.
Design for speed. Automate approvals wherever the risk profile supports it. Set up clear escalation paths for requests that require human review, with SLA expectations that align with the work's urgency. For most routine JIT requests, approval should take seconds.
Set expiration windows that match real work patterns
A two-hour window for a one-time maintenance task is appropriate. A 30-day window for a contractor engagement is also JIT. What matters is that the window is bounded, intentional, and tied to actual work patterns. Arbitrary short windows that do not match how work gets done will generate constant re-requests, which is noise and friction with no security benefit. Talk to the teams doing the work before setting expiration windows.
Monitor, audit, and iterate
Log every JIT grant and revocation. Review the patterns regularly. If a specific user is requesting the same access six times a week, that is a signal: either the expiration window is miscalibrated, or that access should be part of their baseline role. JIT governance is iterative. Build in a regular review cycle to identify where the model needs tuning.
How Oleria supports just-in-time access
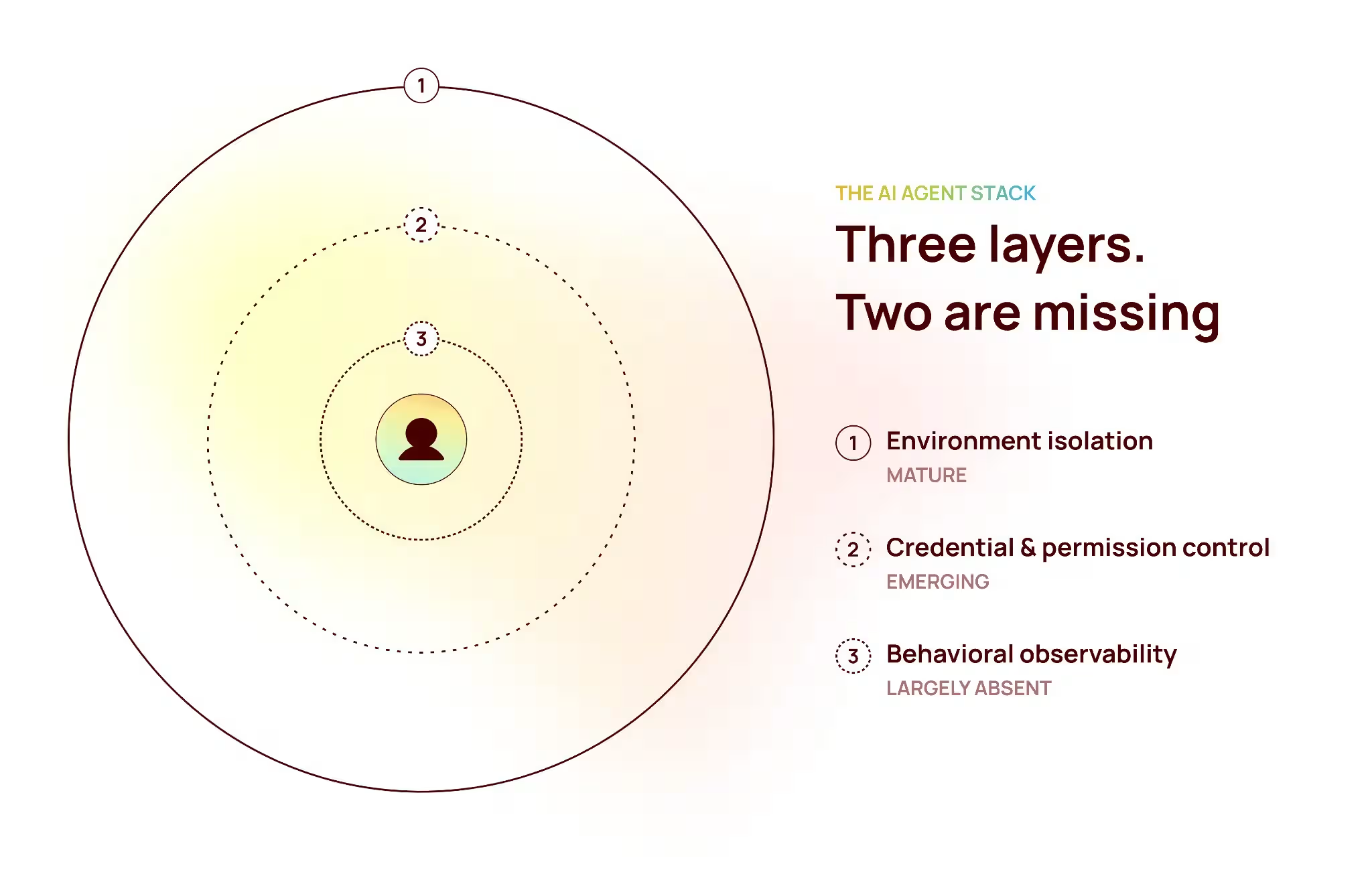
Just-in-time access is a key part of where identity security is heading. But JIT only works if you understand your current access landscape first.
Oleria provides that foundation through the Trustfusion platform: deep visibility across human and non-human identities, with usage-aware context that shows which standing privileges actually get exercised. You can see where persistent access exists, who holds it, and how it’s used — so you can prioritize where JIT will have the greatest impact.
That visibility is what most organizations are missing. Without it, JIT becomes guesswork. With it, you can move toward time-bound, policy-driven access with confidence.
If you're evaluating how JIT fits into a broader identity governance strategy, our articles on what IGA is and user access reviews are good starting points. Or explore the Oleria IGA platform to see how the workflows are configured in practice.
Conclusion
Standing privileges are a structural liability. Most enterprises have built their access models on the assumption that persistent access is a prerequisite for operational efficiency. It's not. JIT access shows you can have both security and speed. The trade-off is in how you design the workflows, not in whether the model is viable.
The direction identity security is heading is clear: continuous, policy-driven access governance rather than periodic reviews and static role assignments. JIT access is the operational foundation of that model. The enterprises that get there first will have a meaningfully smaller attack surface and a much cleaner story to tell auditors when they ask who had access to what, and when.