What a 58% IGA failure rate tells us about the future of identity governance
Only 42% of enterprises use IGA — despite it solving their top identity challenges. S&P Global 451 Research analyst Garrett Bekker explains why legacy IGA fails and what modern governance requires.

Featured event: A CISO’s take
Join Jim Alkove and Ramy Houssaini to learn how forward-thinking security teams are addressing Enterprise AI Copilot risks.
Guest blog post by Garrett Bekker, Principal Research Analyst covering Identity and Access Management with S&P Global 451 Research, sponsored by Oleria.
Organizations consistently say their biggest identity management problems are the challenges that identity governance and administration (IGA) are built to solve. Yet less than half actually use IGA today.
That’s the striking disconnect identified by 451 Research’s Voice of the Enterprise (VotE) service. Enterprises cite managing privileged access, ensuring employees have appropriate access, controlling developer and admin accounts, and running effective user access reviews as their biggest pain points—all textbook IGA and privileged access management (PAM) use cases.2 But only 42% have deployed standard IGA tools.1
What’s holding back IGA adoption? For many organizations, the answer is simple: legacy IGA has too often been expensive, slow, and too complex to justify. Put another way, the pain of change is still worse than the pain of the same.
The IGA tax
Traditional IGA deployments often take 12-24 months, and large enterprises can often spend seven figures on consulting and integration services before the system delivers any value. Add in ongoing maintenance that requires similarly expensive specialized expertise, custom connectors, and constant optimization, and you’ve got a hefty “IGA tax.”
That huge upfront cost and resource commitment leaves an organization locked into a rigid IGA solution, hoping that toolset will remain relevant long enough for ROI to materialize and (eventually) bring them back in the black.
For many, the legacy IGA tax is simply too high to consider.
Simplified solutions fill part of the gap
The market has responded to this problem. Over the past few years, we've seen cloud service providers, identity providers, and PAM vendors all add governance capabilities to their platforms. These offerings try to address the core IGA use cases (user access reviews, compliance reporting, basic provisioning) without the heavyweight deployment model of legacy IGA tools.
For some organizations, particularly smaller businesses facing compliance requirements for the first time, these simplified “IGA Lite” approaches can work. They're faster to deploy, require less specialized expertise, and can cost significantly less than traditional IGA implementations.
Simplified doesn't mean sufficient
Most of these platform-native governance features share common limitations. The ‘original sin’ is that they’re often constrained to a single ecosystem and/or rely heavily on pre-built connectors, which means visibility across hybrid environments can be incomplete. Because those light integrations can often mean a shallow view into identity and access, analytics capabilities tend to be basic — and access reviews become checkbox exercises because reviewers lack the context to make informed decisions.
The dependency on SCIM-based provisioning or APIs creates another bottleneck. Integration with HR systems or multiple identity providers gets complicated quickly. What starts as a simple deployment can turn into a patchwork of partial solutions, each with its own blind spots.
Ultimately, many of the same flaws that plague traditional IGA (think rubber-stamped reviews, incomplete offboarding, orphaned accounts) often persist in these lighter-weight alternatives.
What organizations actually need
Organizations aren’t seeking to water down their actual governance capabilities. To the contrary, more companies are recognizing governance gaps as key business risks. What they want from “IGA Lite” are the core capabilities to solve their governance challenges without the heavy implementation burdens.
Here’s a five-point checklist for what modern, intelligent IGA must deliver:
1) Rapid deployment and practical time-to-value: If it takes 18 months and an army of consultants to get an IGA system running, most organizations will delay or skip it entirely. Implementation should be measured in days or weeks instead of quarters if we want to make adoption feasible for a much broader set of companies.
2) User-aware, context-rich decision support: Access reviews fail when reviewers don't have the information they need to make real decisions. Because without adequate context, even the best-intentioned review process devolves into rubber-stamping. Access reviews should be informed by real usage patterns, peer comparisons, risk signals, dormancy indicators.
3) Unified visibility across hybrid environments: Most enterprises run hybrid environments with applications across multiple clouds, on-premise systems, and SaaS platforms. A modern IGA solution must be able to visualize the identity sprawl problem in order to allow security teams to begin resolving it.
4) Operational scalability: Managing the system can’t be so complicated that only a few specialists can handle it, or that becomes a limiter to practical value. And the ongoing maintenance burden can't be so heavy that it overwhelms the value of the governance capabilities themselves.
5) Realistic total cost of ownership: This includes not just licensing costs but implementation expenses, integration work, ongoing maintenance, and the time investment from internal teams. If the math doesn't work, the project doesn't happen.
The opportunity ahead
The gap between IGA demand and IGA deployment represents both a security risk and a market opportunity. Organizations need solutions that deliver actual governance capabilities (not simplified versions) with deployment and operational models that match how businesses actually work (not how they worked in 2010).
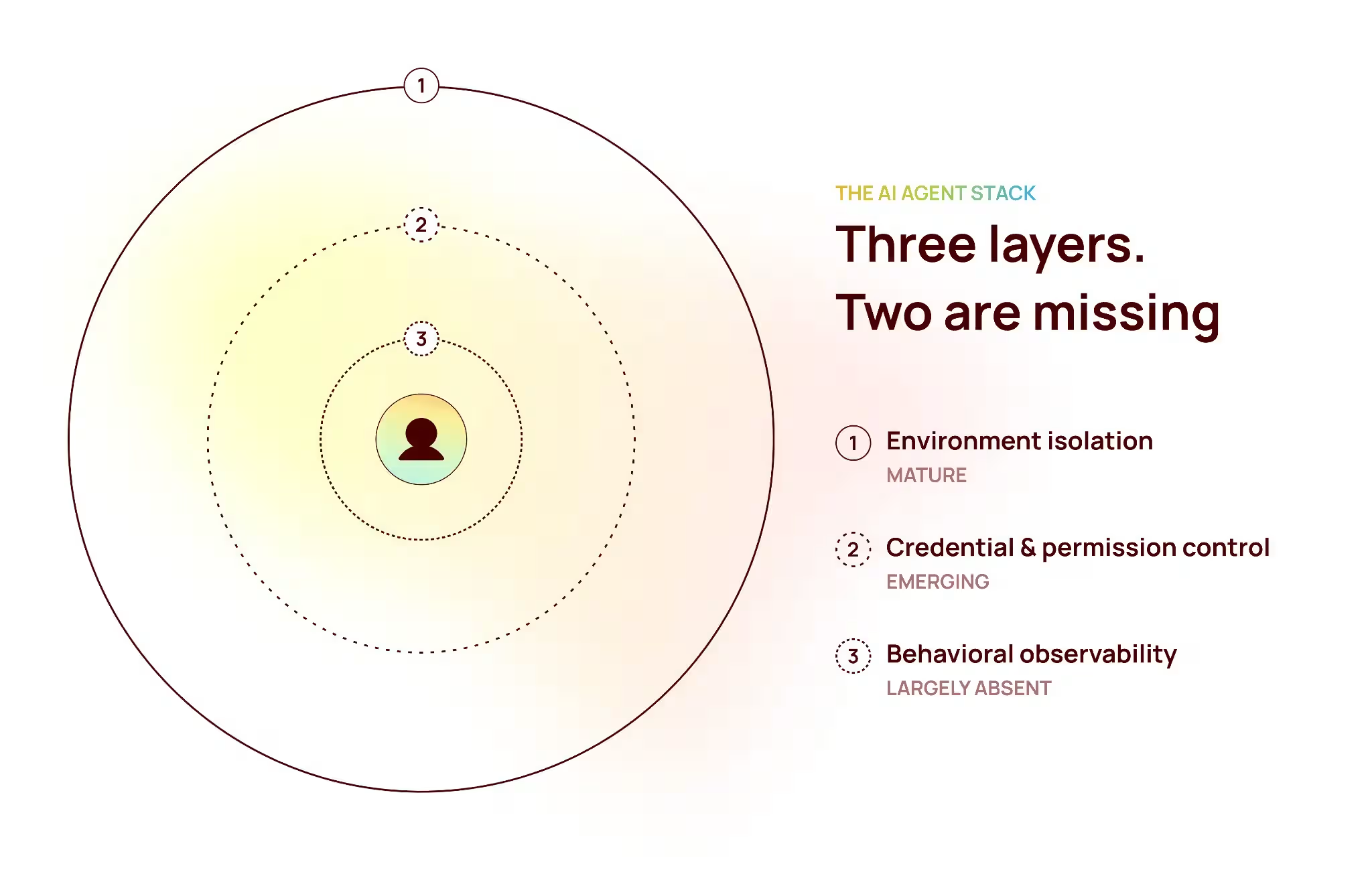
At the same time, identity has expanded well beyond people. Non-human identities (service accounts, API keys, machine identities) and AI agents require complex, machine-speed governance models that legacy IGA architectures were never designed to handle. And the speed and scale of the AI identity problem can make trying to retrofit traditional IGA solutions a dangerous gamble. Solutions that start with a clean-sheet approach may have the advantage.
Some of this will come from technology improvements. Advances in AI and machine learning can help with the manual workflows that make traditional IGA so labor-intensive: access requests, provisioning and deprovisioning, and access review preparation. Better automation here would be genuinely useful, not just a feature bullet.
But here’s the real irony of the “IGA Lite” mandate: modern IGA actually requires vendors to build more, not less.
Delivering governance without the traditional implementation tax means vendors must take on the heavy lift upfront. Vendors need to develop deep integrations, rich data models, and context-aware visibility across hybrid environments. They must do the hard engineering work in advance so organizations don’t have to stitch together connectors, manage custom code, or rely on armies of consultants just to get value.
By shifting that burden from the customer to the platform, modern IGA becomes faster to deploy, easier to operate, and more complete in practice – a powerful as well as practical way to close the IGA gap.
1) 451 Research’s Voice of the Enterprise: Information Security, Technology Roadmap 2025
2) 451 Research’s Voice of the Enterprise: Information Security, Identity Management 2025