Identity security: why IAM alone won't cut it anymore
Discover what identity security is and how it goes beyond IAM. Learn how usage-aware visibility protects against identity-based attacks.

Featured event: A CISO’s take
Join Jim Alkove and Ramy Houssaini to learn how forward-thinking security teams are addressing Enterprise AI Copilot risks.
Organizations have invested heavily in firewalls, endpoint protection, and network security. That strategy worked fine when your perimeter kept threats out. But attackers have shifted tactics, with 88% of web application breaches now involving stolen credentials. Bad actors aren't breaking in anymore; they are logging in.
Here's the problem. Traditional identity and access management (IAM) tools were built for yesterday, not tomorrow. They're leaving massive blind spots that bad actors can exploit and leave organizations at risk.
If you're still treating IAM as a complete solution, you're missing the full picture. Here's why identity security has evolved beyond basic access management and what that means for your organization.
What is identity security?
Identity security is the practice or discipline of protecting every digital identity in your organization throughout its lifecycle. This includes human employees, contractors, service accounts, bots, and AI agents.
Traditional IAM focuses on authentication (verifying who you are) and authorization (granting initial access). Identity security builds on that foundation but addresses what happens after access is granted.
Here's the core difference: IAM answers "Who can access our systems?" Identity security answers "Who is accessing them, what are they doing, and does it represent a risk?"
The problem IAM alone can't solve:
Your identity and access data live in silos. Your IdPs, custom apps, cloud platforms, and HR systems all speak their own language about identity and access. This fragmented data leaves you with incomplete identities. By the time you manually connect the dots, everything has already changed.
And here's what makes this risky: seeing permissions isn't enough. Permissions and entitlements show who can access your systems, but not what they're doing with that access. That gap creates risk, wasted spending, and compliance cycles that never end.
Identity security should answer three questions that IAM can't:
- Who has access to what? Every identity across local and managed environments. Not just your employees, but contractors, service accounts, and non-human identities too.
- How is that access being used? Permissions show what's possible. Usage data shows what's actually happening. You'll see dormant accounts that suddenly wake up, unused privileges creating unnecessary risk, and access patterns that don't match someone's job.
- What risks exist? Real-time visibility into identity activity, excessive permissions, and unusual behavior that might signal a threat.
Why identity security matters
The threat landscape has fundamentally changed. Identity is now the primary way attackers get in. Here's why this matters more than ever:
Your attack surface is exploding.
Over 95% of enterprise permissions go unused (1), leaving open doors that attackers and AI co-pilots can exploit. Dormant accounts become unguarded entryways.
Think about that for a second. As your organization deploys AI tools like Microsoft 365 Copilot, all those dormant permissions suddenly become active vulnerabilities.
And it's not just AI. Non-human identities like service accounts, API keys, and bots are multiplying faster than your security team can track them. These machine identities often run with elevated privileges, making them attractive targets.
Fragmentation creates dangerous blind spots.
Your IdPs, cloud platforms, SaaS applications, and HR systems all speak different languages when it comes to identity and access.
This siloed data leaves you with fragmented identities. By the time your security team manually connects the dots across all these systems, the situation has already changed.
Attackers love these gaps. They move laterally through your environment while you're still trying to figure out what's happening.
Seeing permissions isn't nearly enough.
Traditional tools show you who can access your systems. But they don't show you what people are actually doing with that access.
That gap creates real problems. Risk you can't quantify. Wasted spending on unused licenses. Endless compliance cycles that feel like checking boxes.
Without usage-level visibility, you're flying blind on the threats that matter most. Dormant accounts are suddenly activating. Contractors are still accessing systems months after their projects ended. Employees touching sensitive data they have no business reason to see.
Compliance requirements keep getting stricter.
SEC cybersecurity disclosure rules, cyber insurance requirements, and privacy regulations all demand the same thing now: demonstrable evidence.
You need to show you're actively monitoring identity risks. Having governance policies written down isn't enough anymore. Organizations need continuous compliance evidence, not just point-in-time audit snapshots.
The bottom line is clear. Identity has become the primary battlefield. If you're treating IAM as "good enough," you're exposed to the exact attack vectors causing the most damage right now.
Core components of identity security
Modern identity security requires more than creating accounts and managing passwords. Here's what actually matters:
Unified identity visibility
You can't secure what you can't see. That's not just a saying, it's the reality most security teams face every day.
Identity security platforms aggregate identity data from all sources into a single, clear view. This means understanding every identity (human, non-human, and AI), every permission they hold, and every resource they can touch across your entire environment.
No more jumping between different tools trying to piece together the full story.
Usage-based access intelligence
This is where identity security truly differs from everything else.
Traditional IAM shows permissions and entitlements. In other words, who can access what. Identity security reveals actual usage. Who is accessing what, and when?
Oleria goes deeper than just permissions. It shows which accounts are active, which are dormant, and which permissions are never used. This lets you spot and fix real risk immediately, not just theoretical exposure.
Identity lifecycle management
Secure identity practices cover the complete journey. Granting access when someone joins. Adjusting privileges when roles change. And critically, removing access the instant someone leaves.
Automated lifecycle management makes this happen at the speed your business actually moves. Access gets granted right away based on policy. It gets revoked in seconds when it's no longer needed.
Access requests
Waiting days or even weeks for access creates frustration and workarounds.
Modern identity security can automate access requests with intelligent workflows. Employees request what they need. The system routes to the right approvers based on risk level and policy. And AI can assist by recommending appropriate access based on role, department, and actual usage patterns from similar users.
This results in faster provisioning, better security decisions and full audit trails without the manual overhead.
Access reviews
Nobody wants to rubber-stamp thousands of access reviews. It's tedious, time-consuming, and frankly, it doesn't reduce risk.
Modern identity security uses AI-driven intelligence to transform access certifications. Instead of just listing permissions, it provides context. "Last login: 6 months ago." "Permission never used." "Access violates separation of duties."
This turns checkbox exercises into actual risk reduction.
Continuous risk detection and remediation
Identity security platforms continuously monitor identity behavior for potential issues. Privilege escalation attempts. Unusual movement patterns. Dormant accounts suddenly accessing sensitive resources.
Oleria's trusted remediation helps you respond fast. AI-powered, prioritized fixes that are fully tracked, auditable, and reversible. You get insight and action, not just more alerts to sort through.
Resource-level insights
Modern environments demand granular visibility down to the individual resource level. Identity security should answer specific questions, such as "Who shared, copied, and downloaded this file?" Not just "Who has access to this folder?"
This level of detail matters for investigations, incident response, and proving compliance with data protection requirements.
Identity security vs IAM vs IGA
The terminology gets confusing fast. Let's break down what each one actually does:
Identity and access management (IAM) is your foundation.
IAM systems handle the basics. Authentication (proving who you are) and authorization (deciding what you can access). They also manage user lifecycle provisioning.
Think of IAM as your gatekeeper. It controls who gets in and what permissions they have by default.
The limitation? IAM typically stops once it grants access. After a user has credentials and permissions, traditional IAM offers limited visibility into how that access gets used.
Identity governance and administration (IGA) adds policy and compliance.
IGA platforms focus on access certifications. These are the regular reviews checking who has what access. They also handle role management, separation-of-duties controls, and compliance reporting.
IGA answers questions like "Who can access this system?" and "Are we meeting regulatory requirements?"
IGA's strength is making sure the right people have the right access for the right reasons.
The gap? Traditional IGA focuses on entitlements. It shows who can access resources based on their permissions. But it doesn't reveal who is accessing them or how those permissions get used in practice.
Identity security brings them together.
Identity security includes IAM and IGA capabilities but adds what's been missing: usage-aware visibility and real-time threat detection.
Identity security platforms unify identity data across your entire environment. They enrich it with activity insights and continuously monitor for threats.
Here's how they work together in practice:
IAM provisions a contractor with access to your cloud environment when they start their project.
IGA includes that access in quarterly certification reviews to check if it's still needed.
Identity Security reveals the contractor account went dormant three months ago, then suddenly started accessing sensitive resources at 2 AM from an unusual location. It triggers an immediate alert for investigation.
These aren't competing approaches. They're complementary. IAM and IGA create the structure. Identity security provides the visibility and threat detection that makes that structure actually secure.
Common identity security challenges
Even organizations that recognize the need for stronger identity security run into real obstacles:
Fragmented identity data.
Your IdPs, custom applications, cloud platforms, SaaS tools, and HR systems each keep their own version of identity truth. Often with inconsistent naming and conflicting information.
This fragmentation doesn't just slow you down. It creates blind spots where real security gaps hide.
Data quality concerns.
Many identity security initiatives never get off the ground. Why? Organizations think they need perfect data before they can start.
Here's the reality. Most enterprises have messy identity data. Orphaned accounts from past acquisitions. Conflicting authoritative sources. Incomplete information is scattered everywhere.
Traditional identity tools demand clean data to function. This creates an impossible situation. You need visibility to clean the data, but you need clean data to get visibility.
The visibility gap between permissions and usage.
Knowing who can access a system tells you nothing about who is accessing it.
This gap means you miss the threats that matter. Dormant admin accounts that suddenly activate. Contractors who still have access months after their projects ended. Service accounts with elevated privileges are being actively exploited.
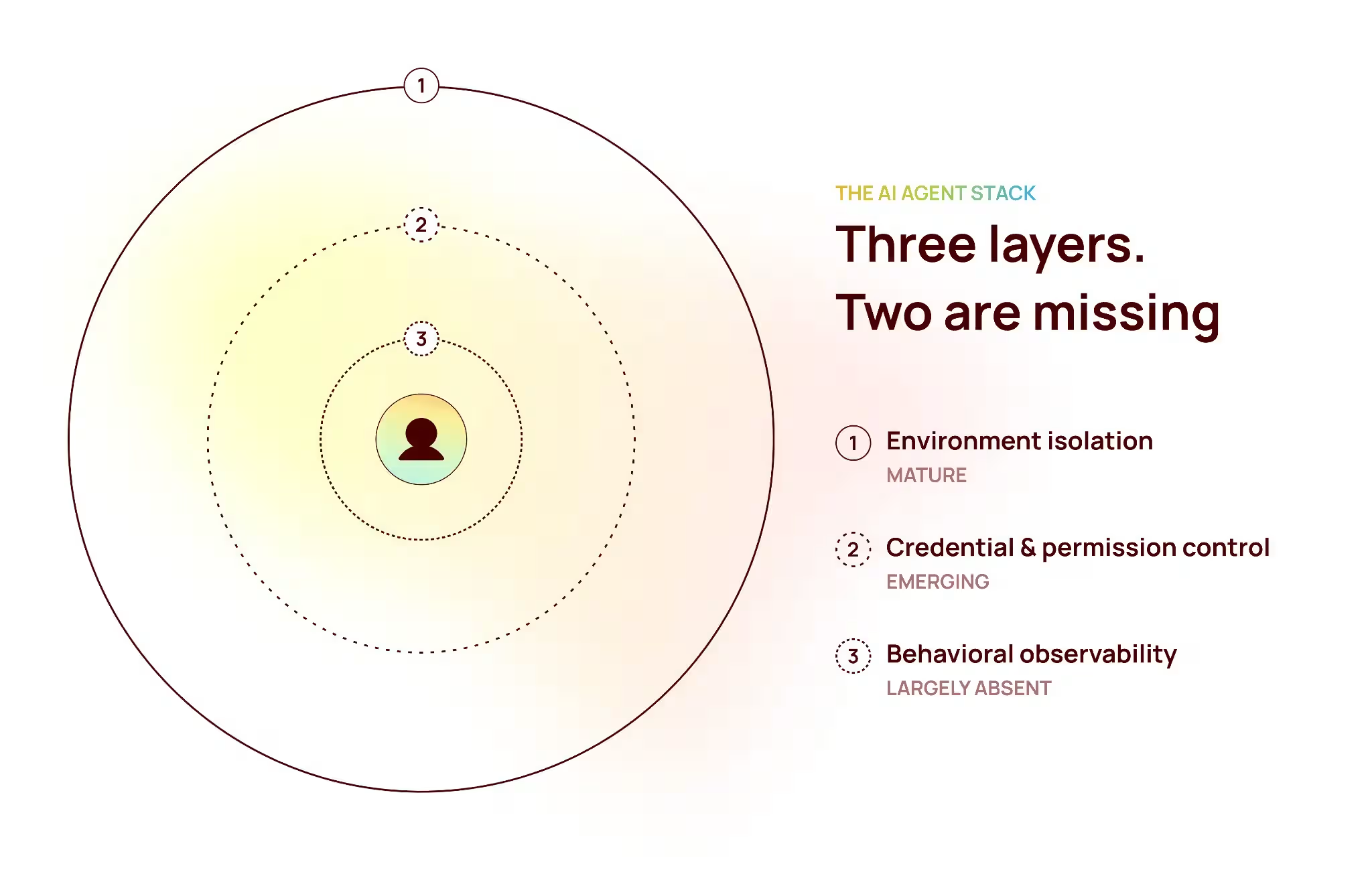
Non-human identity explosion.
Service accounts, API keys, bots, and AI agents now far outnumber human identities in most environments.
These machine identities create unique challenges. They often run with elevated privileges. They rarely need multi-factor authentication. And they almost never appear in access certification campaigns.
Yet they're increasingly the targets attackers focus on. Why? Because they provide persistent access without the behavioral signals that might flag a compromised human account.
Slow and expensive implementation timelines.
Traditional identity governance tools typically take months to deploy. They need extensive customization and significant professional services spending.
Even after deployment, these systems struggle with adoption. They don't provide immediate value and require constant manual maintenance to remain useful.
Proving ROI.
Security leaders face a communication challenge. How do you translate identity risks into business language that resonates with CFOs and boards?
Too often, this challenge goes unresolved until a breach happens. By then, it's too late.
Identity security best practices
Building a mature identity security program takes more than just buying tools. Here are the practices that actually work:
Start with unified visibility.
You can't secure what you can't see. It's that simple.
Your first step is to establish a single source of truth for all identities across your environment. Pull together data from every IdP, directory, cloud platform, SaaS application, and HR system into a unified view.
Here's the key. Don't wait for perfect data. Identity security platforms like Oleria close your visibility gaps with a single platform that gives you full clarity and control over every identity – human, non-human and AI.
Monitor usage, not just permissions.
Stop focusing only on what users can do. Start watching what they are doing.
Set up continuous monitoring that shows which accounts are active versus dormant. Which permissions actually get used? Which access patterns deviate from normal behavior?
This shift from theoretical to actual changes everything about how you assess and manage risk.
Enforce least privilege continuously.
Least privilege isn't something you configure once and forget. It's an ongoing practice.
Regularly adjust permissions based on real usage data. If someone hasn't accessed a system in 90 days, that's your signal to review whether they still need it.
Automate identity lifecycle management.
Manual provisioning and deprovisioning are too slow. They're also too prone to human error.
Automated workflows grant access immediately when employees join or change roles. More importantly, they revoke access instantly when someone leaves your organization.
This automation closes the "lever gap" from weeks down to seconds.
Simplify access reviews with context.
Stop asking managers to approve thousands of permissions they don't understand.
Instead, provide context for every access certification. "Last used: Never." "Last login: 6 months ago."
When reviewers have usage data and risk indicators, they can make real decisions rather than just clicking 'approve' to clear their queue.
Secure non-human identities.
Service accounts, API keys, and machine identities need governance too.
Assign clear ownership to every non-human identity. Enforce credential rotation. Monitor their activity for unusual patterns. Include them in your access reviews.
Prepare for AI deployments by securing access first.
Before you roll out AI assistants, audit what data those systems will access and have access to.
Here's what you need to remember: 95% of permissions sit unused until an AI discovers them.
Clean up overprivileged access. Remove dormant accounts. Do this before deployment, not after.
Maintain continuous compliance.
Regulations and cyber insurance requirements increasingly expect continuous monitoring, not annual audits.
Set up automated evidence collection. Real-time compliance reporting. Audit trails that document every access decision.
This shifts you from being reactive to audits to maintaining always-on compliance readiness.
How to evaluate identity security solutions
If you're looking to update your identity security platform, here are a few key things to consider:
Demand usage-level visibility, not just permission data.
Ask vendors to show you in a live demo (not slides) how they reveal which accounts are actually active, which permissions get used, and which access patterns represent risk.
If they only show who can access resources but not who is accessing them, you're looking at a governance tool, not a security platform.
Test how the solution handles messy data.
Bring your actual data into a proof-of-concept. All the inconsistencies, fragmentation, and legacy issues are included.
Can the platform unify identities across disconnected systems? Does it provide value right away, or does it demand months of data cleanup first?
Solutions that need perfect data hygiene to function will stall your initiative before it starts.
Check the time to first value.
Ask how long from first login to actionable insights. Days? Weeks? Months?
Modern identity security platforms should surface critical risk findings quickly. Dormant accounts with recent activity. Excessive permissions. Compliance gaps.
If the vendor talks about six to eighteen-month implementation timelines and extensive professional services, you're looking at legacy architecture.
Verify resource-level granularity.
Many platforms claim "fine-grained access control" but only deliver folder-level or application-level visibility.
Push vendors to demonstrate resource-level insights. "Who shared, copied, or downloaded this specific file?" "Which identities accessed this particular storage bucket?"
If they can't answer at that level of detail, their solution won't effectively support investigations or data protection requirements.
Check non-human identity coverage.
Ask how the platform discovers, governs, and monitors service accounts, API keys, bots, and AI agents.
Can it identify which machine identities exist across your environment? Track their activity? Detect unusual patterns in their behavior?
If the solution only focuses on human users, it's missing the fastest-growing part of your attack surface.
Test response speed and audit trails.
When the platform spots a risk (a dormant account suddenly activating, a privilege violation, excessive permissions), how quickly can you respond?
Can you revoke access in seconds? Is every action fully tracked, auditable, and reversible?
Insight without fast, confident action just adds to your alert backlog.
Check ease of use.
Get access to the actual interface your teams will use every day. Not a demo environment. The real thing.
Is it intuitive, or does it need extensive training? Can your team find answers quickly, or do they have to dig through complex menus?
Powerful platforms that nobody uses deliver zero value.
Test solutions with your specific use cases.
Don't let vendors drive the demo with their favorite features. Bring your actual problems.
"Show me how you'd find all contractors who still have access 90 days after their projects ended."
"How would you identify service accounts with privileged access they've never used?"
"Can you show which identities accessed this sensitive dataset last month?"
Vendors comfortable with your real scenarios are far more likely to deliver after you buy.
The future of identity security
Identity security is evolving fast. Here's where it's heading:
Identity will become the primary security control.
Zero-trust architectures are replacing traditional perimeter-based security. This means identity verification and context-aware access policies move to the center of everything.
Every access decision will factor in identity risk scores, device posture, and behavior patterns. Not just username and password.
AI will play two roles at once.
Security teams will increasingly rely on AI to analyze identity patterns and detect problems faster than any human analyst could.
At the same time, AI agents will dramatically expand your attack surface. They'll access data at machine speed with permissions beyond those granted to their human creators.
Organizations that ignore this dual reality will struggle.
Usage-aware governance will become the baseline.
The market is moving away from permission-only approaches. Buyers want usage-based platforms that show actual risk, not just theoretical access.
Boards and regulators will demand evidence you're actively monitoring how access gets used. Not just that you have governance policies written down somewhere.
Real-time becomes expected, not exceptional.
Batch processing and nightly updates won't meet the bar anymore.
Security teams will expect identity platforms to reflect changes the moment they happen. Continuous risk assessment that updates as your environment evolves.
The organizations that will succeed are investing now in usage-aware identity security platforms. They're treating identity as a continuous security operation, not a quarterly governance task.
Identity security starts with visibility
Identity-based attacks aren't slowing down. Compliance requirements aren't getting easier. Your attack surface isn't shrinking.
The gap between what traditional IAM shows you and what's actually happening? That's where the most damaging breaches start.
Here's the good news. You don't need perfect data or massive implementation projects to close that gap. Modern identity security platforms work with your reality and deliver visibility in hours, not months.
Your identities are already accessing your most sensitive resources right now. The question is whether you can see what they're doing and respond fast enough when something looks wrong.
1) Microsoft Security, 2021 State of Cloud Permissions Risks Reports