Identity security vs. IAM vs. IGA: Understanding the differences
IGA vs IAM: understand how access management and governance differ, where each fits, and how identity security builds on both to reduce risk across human and non-human identities.

Featured event: A CISO’s take
Join Jim Alkove and Ramy Houssaini to learn how forward-thinking security teams are addressing Enterprise AI Copilot risks.
Identity is the foundation for access in your environment, and terms like identity security, identity and access management (IAM) and identity governance and administration (IGA) are making their way out of IT into conversations across the rest of the business. But these terms are not interchangeable. The differences matter when you are trying to reduce real risk, not just add another tool.
What is identity security?
Identity security is the practice of protecting your organization by managing who or what can access resources, where and when, based on context and risk. Even if credentials are compromised, identity security seeks to limit potential damage.
It represents a broad approach. Rather than only asking, “Does this identity have the right role?”, identity security considers:
- Who or what is this identity really
- What can it access across all systems
- How is that access actually being used
- Does this behavior make sense given context and risk
Identity security looks across:
- Human users such as employees, contractors, and partners
- Non-human identities such as service accounts, APIs, bots, and AI agents
- Access paths such as SSO, local accounts, shared secrets, and tokens
- Real activity, such as which permissions are used and which are just sitting there
We explore identity security in depth here.
Traditionally, organizations relied on IAM and IGA to address these identity security concerns. However, with the rise of AI tools, SaaS adoption, and numerous non-human identities, legacy IAM and IGA are insufficient. A continuous, contextual view of identities and access is now required, beyond static roles and periodic reviews.
In the AI era, identity security must become: 1) right sized, 2) based on actual need and usage, and 3) monitored continuously for risky behaviors.
What is identity and access management (IAM)?
Identity and access management (IAM) addresses a key question: “Can this identity log in and access this resource?” IAM encompasses the processes and technologies that create and manage digital identities, authenticate those identities, and authorize what they can access
Common IAM capabilities include:
- Directories and identity stores
- Single sign-on (SSO)
- Multi-factor authentication (MFA)
- Role-based access control (RBAC)
- Federation across systems and clouds
When IAM is working well, organizations see key outcomes:
- Consistent logins instead of multiple separate accounts
- Central policies instead of one-off decisions in each application
- Stronger authentication instead of passwords alone
IAM is a necessary infrastructure, but on its own, it does not tell you whether your environment is over-permissioned or whether your AI assistants can see far more than they should. That’s in part because IAM alone has several limitations:
- It is often based on roles and groups, not on how access is actually used
- It struggles with the rapid growth of SaaS tools and non-human identities
- It was not designed for AI agents that can move through data in complex ways
What is identity governance and administration (IGA)?
Identity governance and administration (IGA) manages the lifecycle and oversight of identities and their access. We explore the concept in depth here.
While IAM manages authentication and access enforcement, IGA ensures access remains appropriate over time and is auditable for stakeholders.
Typical IGA capabilities include:
- Joiner, mover, leaver processes (provisioning and deprovisioning accounts; updating access when people change roles)
- Access requests and approvals
- Periodic access reviews and certifications
- Policy enforcement such as the separation of duties
- Audit trails and compliance reporting
IGA answers questions like:
- Who approved this access and when?
- Does this access still make sense given the person’s role?
- Can we prove to auditors that only the right identities can reach critical systems?
As regulations increase and boards demand greater oversight of access risk, IGA enables organizations to establish repeatable and auditable identity programs.
Identity security vs. IAM vs. IGA: How they differ
All three practices center on identity, but they are not interchangeable. Their differences are evident in scope, focus, and outcomes.
Another way to put it:
- IAM gets people and systems into applications
- IGA makes sure that access is appropriate and properly reviewed
- Identity security prevents the environment from becoming over-permissioned and detects risky behavior
Why identity security matters more with AI and LLMs
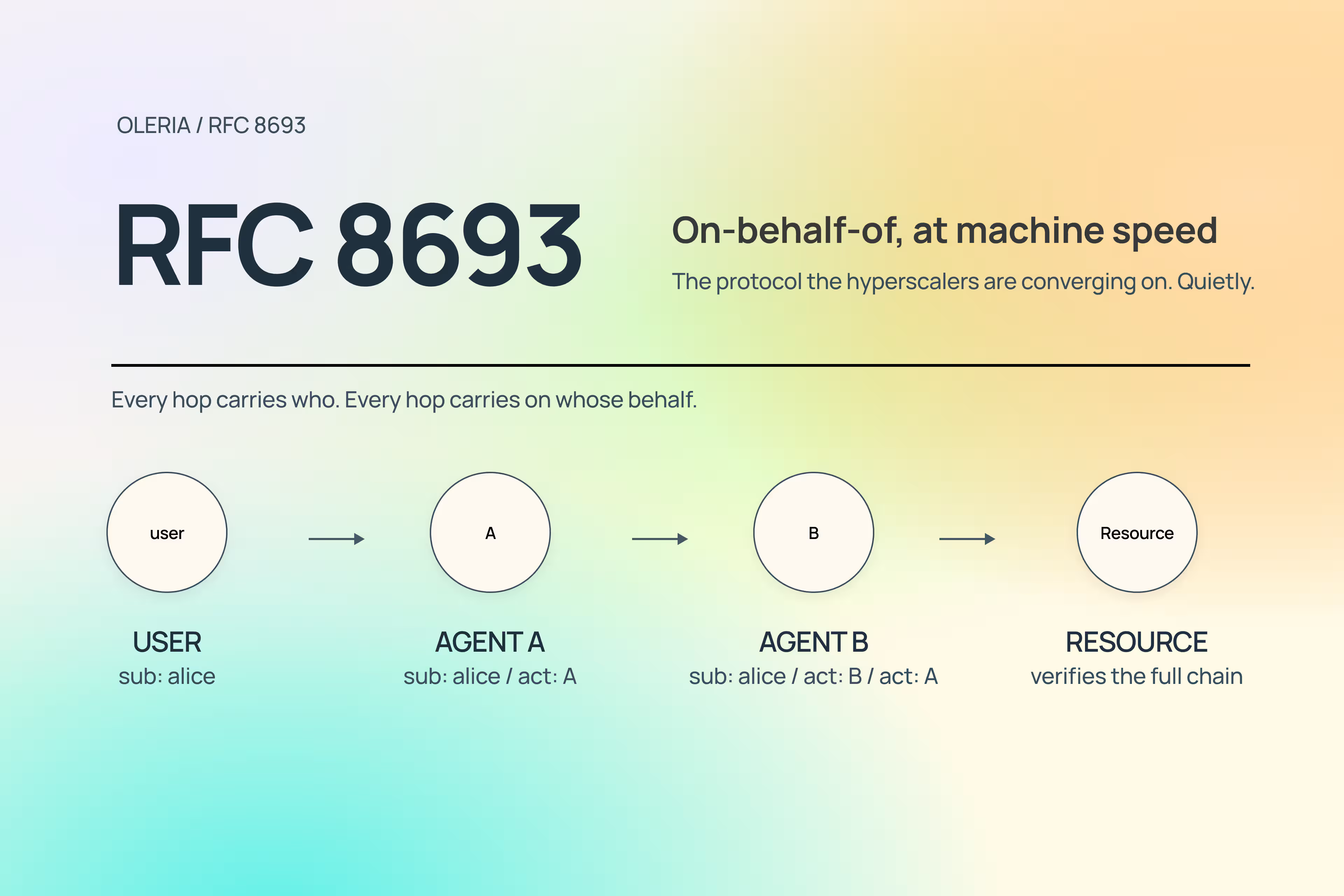
AI does not create new permissions, but leverages existing ones at greater scale, speed, and depth than humans.
A few realities to keep in mind:
- AI copilots and LLM-based assistants are good at finding and connecting information across systems
- Over permissioned accounts that felt low risk with a human user behind them can become high risk when an AI agent can use that same access
- Non-human identities, such as scripts, bots, connectors, and AI services, often outnumber human identities and typically have broad, long-lived access.
In this setting:
- IAM still controls login flows and basic policy enforcement
- IGA still shows that sensitive access is approved and reviewed
- Identity security provides safeguards to prevent AI-powered access from increasing risk in ways that may not be immediately visible.
This includes:
- Understanding the full chain of access for both people and AI agents
- Continuously trimming unused and unnecessary permissions
- Detecting unusual patterns across both human and non-human identities
- Treating AI systems and automations as identities with owners, scope, and review requirements
Without this approach, organizations may complete access reviews yet still leave open pathways to large-scale data exposure through AI-assisted access.
Data and decision models
Each area relies on different inputs to enforce rules and permissions:
- IAM is mostly configuration and role-based. Decisions are based on what is in the directory or IAM policy.
- Example: “This user is in the Finance group, so they get these applications.”
- IGA adds governance information. Decisions are connected to policy, workflow, and audit requirements.
- Example: “This role requires additional approval and this access must be reviewed regularly.”
- Identity security brings context and behavior. Instead of one-time yes-or-no access checks, identity security focuses on ongoing, risk-aware decisions and continuous cleanup of unnecessary or risky access.
- Which privileges are used and which are never touched
- Which combinations of access create risky situations
- How access compares to similar roles and peers
- How human identities behave compared to non-human ones
- Environmental signals such as location, device, and time
Ownership and responsibility
Ownership varies by organization, but common patterns include:
- IAM is often owned by security engineering, infrastructure, or a dedicated identity team
- IGA is usually driven by compliance, risk, or identity governance teams, with business managers as reviewers and approvers
- Identity security sits at the CISO or central security leadership level, because it looks at identity risk end-to-end across tools, clouds, and AI initiatives
In practice, these groups need to work together. IAM and IGA produce important signals. Identity security is where those signals are combined, understood, and acted on.
How identity security builds on IAM and IGA
Most organizations are not starting from scratch. You likely already have:
- One or more IAM platforms
- Some established governance processes and reviews for high-risk systems
- Manual or semi-automated access reviews
Identity security does not replace these systems; it builds upon them.
Here is how that usually looks.
1. Unify identity and access data
Instead of treating each IAM tool or application as its own island, identity security brings together:
- Accounts and entitlements from directories, SaaS, and cloud platforms
- Human and non-human identities
- Activity and usage data across systems
This unified view turns scattered records into a consistent understanding of who can do what, across your environment.
2. Add continuous context
Once you have a unified picture, you can add context like:
- Which privileges are never used
- Where access patterns do not match a person’s role
- Where non-human identities have very broad, long-lived access.
- Where AI agents have more access than is actually needed
This context makes least privilege achievable. Rather than guessing, you can identify which permissions to remove and where to focus efforts.
3. Drive risk-based action
Identity security focuses on:
- Automatically flagging high-risk access based on context and behavior
- Prioritizing the most important issues to fix
- Feeding better information into existing IAM and IGA workflows
- Making reviews and certifications more meaningful and less manual
IAM grants necessary access. IGA ensures that access is governed and auditable. Identity security maintains a healthy environment and reduces accumulated risk over time.
Where IAM, IGA, and identity security each help most
It can be helpful to map common problems to each area.
You likely need to focus on IAM when:
- Users manage many passwords and separate accounts
- You do not have MFA on sensitive systems
- You are rolling out new SaaS platforms and need consistent SSO and policies
You lean on IGA when:
- Auditors are asking for clear evidence of who can access what
- Role changes and offboarding are slow or inconsistent
- Business owners are approving access reviews without much context
You need identity security when:
- You suspect your environment is over-permissioned but cannot quantify it
- Non-human identities and service accounts have grown beyond what you can track
- AI assistants and automations can see more data than you are comfortable with
- You want ongoing assurance that least privilege is actually happening in practice
Most organizations advancing in this area require all three. Over time, identity security becomes the unifying layer that integrates IAM and IGA.
How to assess where you are
If you are trying to decide what to improve next, it can help to ask three simple questions.
- Do we have a solid IAM foundation?
- Do we have SSO and MFA on critical systems
- Do we have centralized identity stores
- Do we use groups or roles in a consistent way
- Do we have structured IGA practices?
- Are joiner, mover, and leaver processes defined and followed
- Do we have clear owners and approvers for access requests
- Do we regularly review access to high-risk systems and document those reviews
- Do we have true identity security capabilities?
- Can we see all identities and entitlements, both human and non-human
- Do we understand which access is actually used
- Can we detect and reduce over-permissioning on an ongoing basis
- Do we have coverage for AI agents, APIs, and automations, not just people
Perfection in each area is not required to make progress. However, focusing solely on IAM and IGA without considering identity security may result in managing access without fully addressing risk.
Bringing it all together
IAM, IGA, and identity security are connected, but different:
- IAM makes access work
- IGA makes access governed and auditable
- Identity security ensures access remains safe, right-sized, and sustainable as your environment and use of AI evolve.
As software, automation, and AI agents increasingly act on behalf of people, identity will remain the primary vector for risk. Organizations that succeed will treat identity security as a core function, integrating IAM and IGA rather than managing them as separate initiatives.
Start with an identity security assessment to understand your current risks across human, non-human, and AI identities, and where IAM, IGA, and identity security can work better together.
If you are ready to see what this looks like in practice, you can also request a personalized demo to walk through how a unified view of identities, access, and behavior can help you move toward true least privilege and reduce identity-driven risk over time.