Oleria's Identity Security Assessment
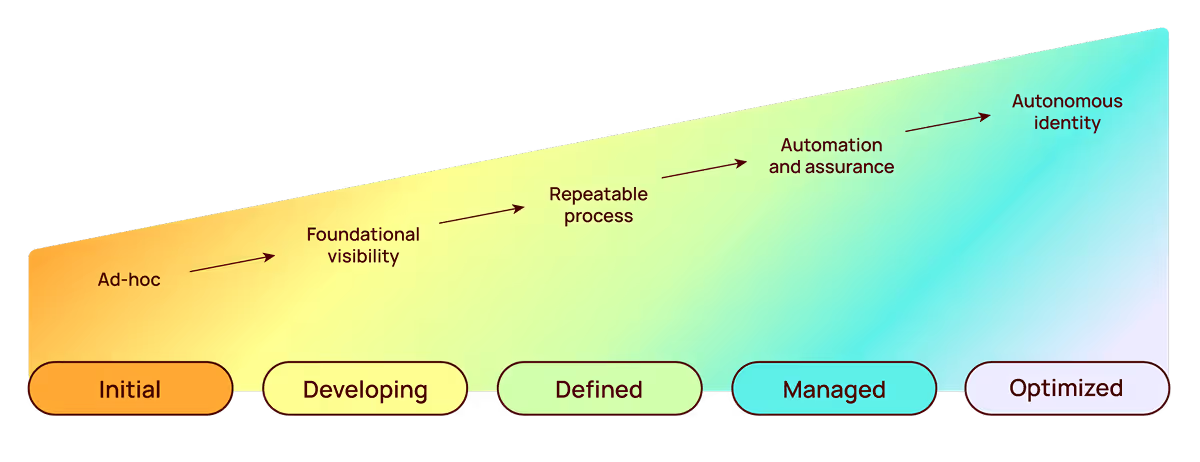
Accurately assess, benchmark and optimize your security posture leveraging our industry-backed identity maturity model.
.svg)
.avif)
.avif)
How it works
Over an 8-week engagement, you'll receive a detailed report and an executive briefing that lays out the necessary steps to improve your organization’s identity security. Armed with this actionable plan, you can then decide whether to leverage our optional expert remediation service to immediately address your top risks and accelerate your security journey.
Week 1-7: Assessment + analysis
Week 8: Report + executive briefing
Optional: Professional remediation services
Your tailored path forward.
We benchmark your current program against our industry-backed identity security maturity model. Know exactly where you stand and get a customized roadmap toward an optimized security strategy.
See what's possible with
Oleria Identity Security
Govern with intelligence and automation
Autonomous identity governance that continuously enforces least-privileged access.
Accelerate incident investigation
Proactively monitor, trace, and respond to identity threats.
Remediate rapidly with precision
Precisely disable accounts, revoke access, or remove users with full context.
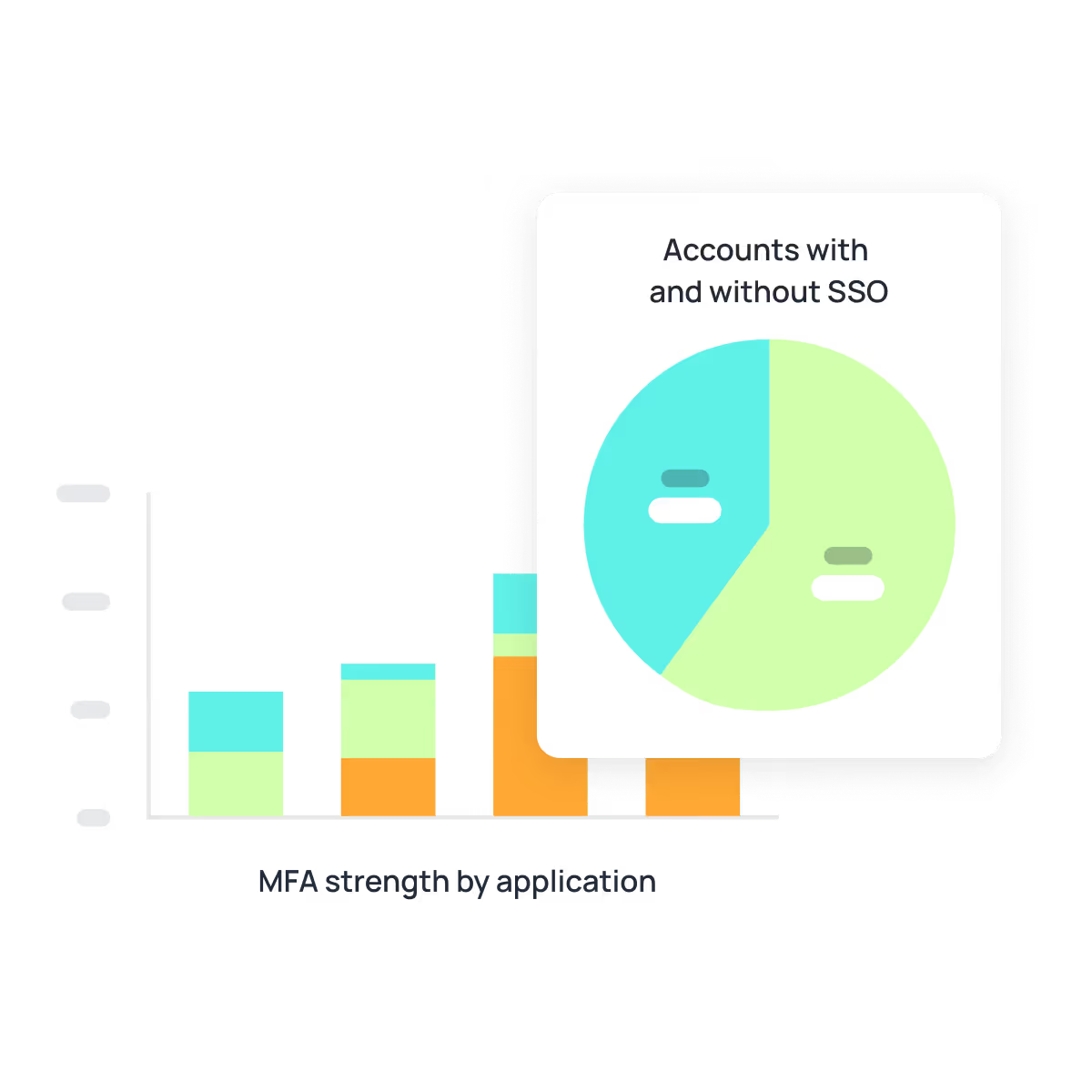
See every identity—all in one place
See the complete picture of access and activity in one view—who created each identity, what it touches, how it's used, what to fix.
.avif)
.avif)