The context graph that governs everything
The identity context graph connects identities, resources, policies, and approvals into a single queryable structure — so enterprises can finally explain not just who has access, but why.
.webp)
Featured event: A CISO’s take
Join Jim Alkove and Ramy Houssaini to learn how forward-thinking security teams are addressing Enterprise AI Copilot risks.
Most enterprises know who has access to what. Almost none can explain why. The identity context graph is built to answer both.
Context Layer is the new security layer.
Every enterprise runs on a deceptively simple question: who has access to what, and why?
It sounds like something that should have been solved decades ago. We've had directories since the 90s. Identity governance platforms since the 2000s. Cloud security tools for the last ten years. Billions of dollars spent. And yet, ask any CISO to explain how a specific contractor got admin access to a production database, what policy allowed it, who approved the exception, and whether that exception is still valid, and watch what happens.
They can't answer it. Not because they're not good at their jobs. Because the answer doesn't live in any single system. It's scattered across an identity provider, a cloud console, a ticketing system, a Slack thread where someone said "yeah, go ahead and grant it," and a policy document that was last updated eighteen months ago. The what of access lives in systems. The why – the decision, the context, the reasoning – was never captured as data in the first place.
This is the problem that shaped how we built Oleria. Not "how do we build a better access review tool." But: what if the connective tissue between identities, resources, policies, business rules, approvals, and exceptions was a living, queryable structure – a graph you could actually traverse, question, and reason over?
What an identity context graph actually looks like
Think about what connects an identity to a resource in the real world. It's not a row in a spreadsheet. It's a chain: a person joined a team, inherited a role, that role carried entitlements across six applications, one of those entitlements was elevated through an exception approved by a manager who has since left the company, under a policy that was revised last quarter. Every link in that chain carries context: business justification, time, policy version, approval authority, risk signal.
An identity context graph makes all of those links explicit and connected. Identities. Resources. Policies. Entitlements. Approvals. Exceptions. Business rules. Not in separate databases that you reconcile during quarterly reviews. In a single, unified structure where relationships are first-class and the decision trail is preserved.
This means you can ask questions that were previously impossible without weeks of manual forensics: Show me every identity that gained access to this resource through an exception. Show me which of those exceptions were approved under a policy version we've since deprecated. Show me the approval chain and whether the approver still has the authority to grant this level of access.
These aren't hypothetical queries. This is how access actually works in enterprises – messy, contextual, layered with history and human judgment. The graph just makes it visible for the first time.
What changes when you have an identity context graph
This is where it gets interesting. The context graph doesn't just improve existing processes. It fundamentally changes what's possible across every dimension of identity security.
Access reviews transform completely. Today, a reviewer gets a spreadsheet of entitlements and clicks "approve" or "deny" with almost no context. They don't know why access was granted. They don't know if it was an exception. They don't know if the business justification still holds. With a context graph, the review starts with context: here's the decision trail, here's what changed since last review, here's the risk signal. Reviewers make real decisions instead of rubber-stamping.
Remember that contractor from earlier? With the context graph, you traverse the full chain in seconds: the exception was approved by a manager who left in Q3, under a policy version deprecated in January, through a role inherited from a team the contractor was never formally assigned to. That's not a hypothetical — that's a query. One CISO told us that what used to take his team weeks of manual correlation now resolves in seconds. That's the difference between governing access and guessing at it.
Incident response gets a time machine. When something goes wrong, the first question is always "how did this identity get this level of access?" Today, reconstructing that answer is an archaeological dig across five systems. With the context graph, the full lineage is already there – the original grant, every modification, every approval, every policy that applied at each point in time. You're not reconstructing. You're traversing.
Compliance becomes a byproduct, not a project. Auditors don't want spreadsheets. They want evidence of how access decisions were made and whether those decisions followed policy. A context graph produces that evidence as a natural artifact of how access is governed. The audit trail isn't assembled after the fact. It exists because the graph exists. (For a deeper look at why this matters economically, see the true cost of IGA.)
Identity security becomes autonomous. We've long believed that identity security should work like a healthy immune system: continuous, granular, adaptive, always sensing and responding. But an immune system without memory treats every threat like it's brand new. That's how most identity security operates today: reactive, amnesiac, starting from scratch every cycle. The context graph is the memory layer. It's what allows the system to recognize patterns it's seen before, recall how similar access decisions were resolved, and respond with increasing intelligence over time. With a context graph underneath, identity security stops being a periodic review exercise and becomes a living, learning system that gets smarter with every decision it captures.
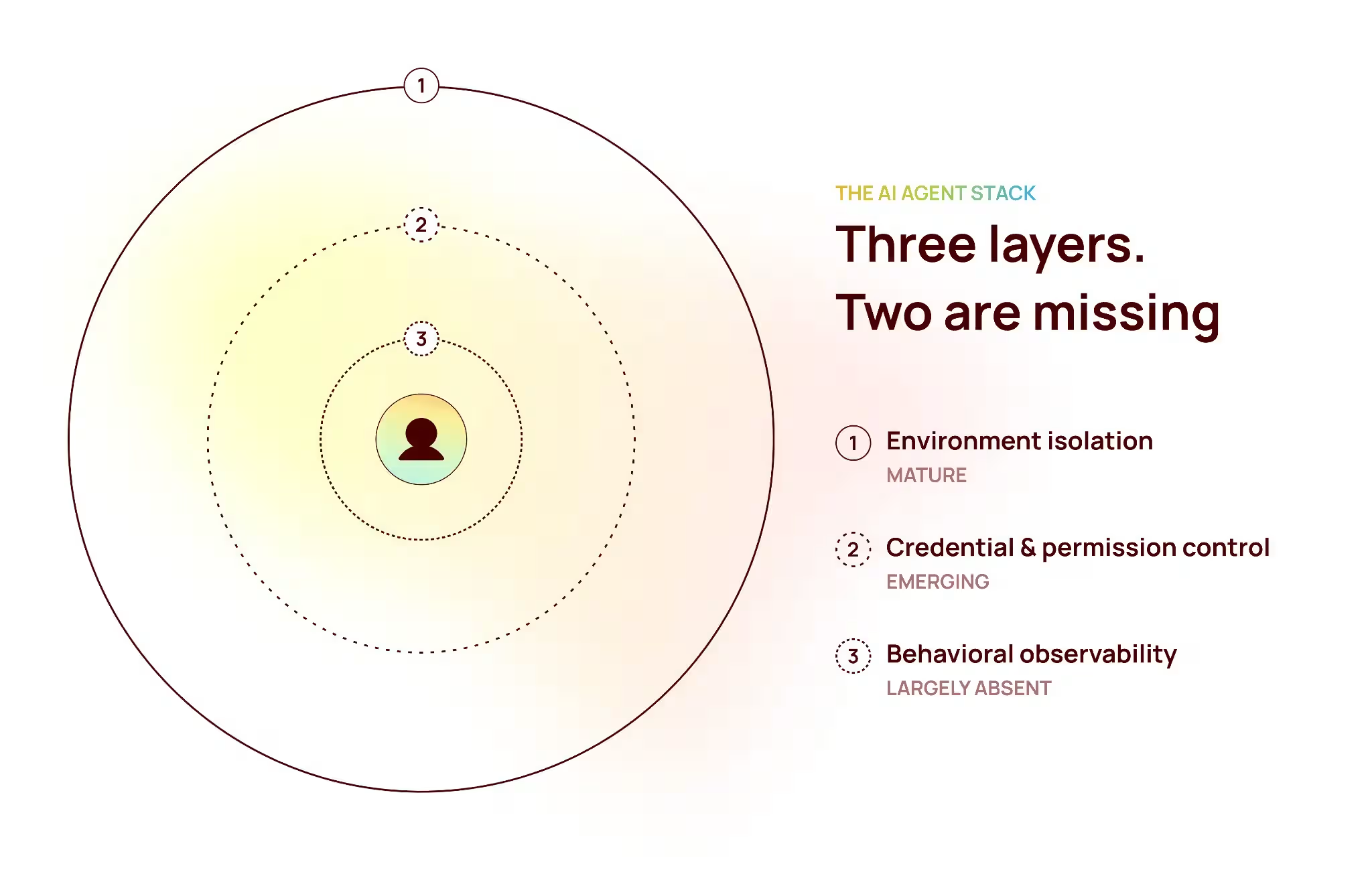
And here's why that matters now more than ever: AI agents. Agents are already requesting access, using credentials, and taking actions across enterprise systems. Every agent is an identity. Every identity needs governance. As agents scale, the volume of access decisions will explode – and the window for human review will shrink toward zero. An immune system that learns from its context graph can govern autonomous access at a scale that no human team or periodic review cycle ever could. Without it, you're flying blind into a world where machines are making access decisions faster than humans can audit them.
Where this is heading: identity governance in the agentic era
Foundation Capital recently published a compelling thesis on context graphs as the next trillion-dollar platform layer: the idea that the most valuable data in the agentic era won't be the records enterprises already keep, but the decision traces they've never systematically captured. We think they're exactly right.
And we think the most important context graph in any enterprise is the one for identity. Because identity is the layer that governs everything else. Every workflow, every agent, every automated decision eventually resolves to a question of access: can this identity take this action on this resource, and should it?
The companies that build this graph – that treat the why behind access as first-class data – aren't just solving a security problem. They're building the governance infrastructure for how enterprises will operate when agents and identities of every kind outnumber the humans managing them.
We've spent the last two years building exactly this. And we're just getting started. If this resonates, we'd love to show you what the identity context graph looks like in practice. Visit us at oleria.com or reach out to start a conversation.