
May 13, 2026
The first AI-operated breach wasn't an AI safety failure. It was an identity governance failure
by
Jagadeesh Kunda

The first AI-operated breach wasn't an AI safety failure. It was an identity governance failure
by
Jagadeesh Kunda
May 5, 2026
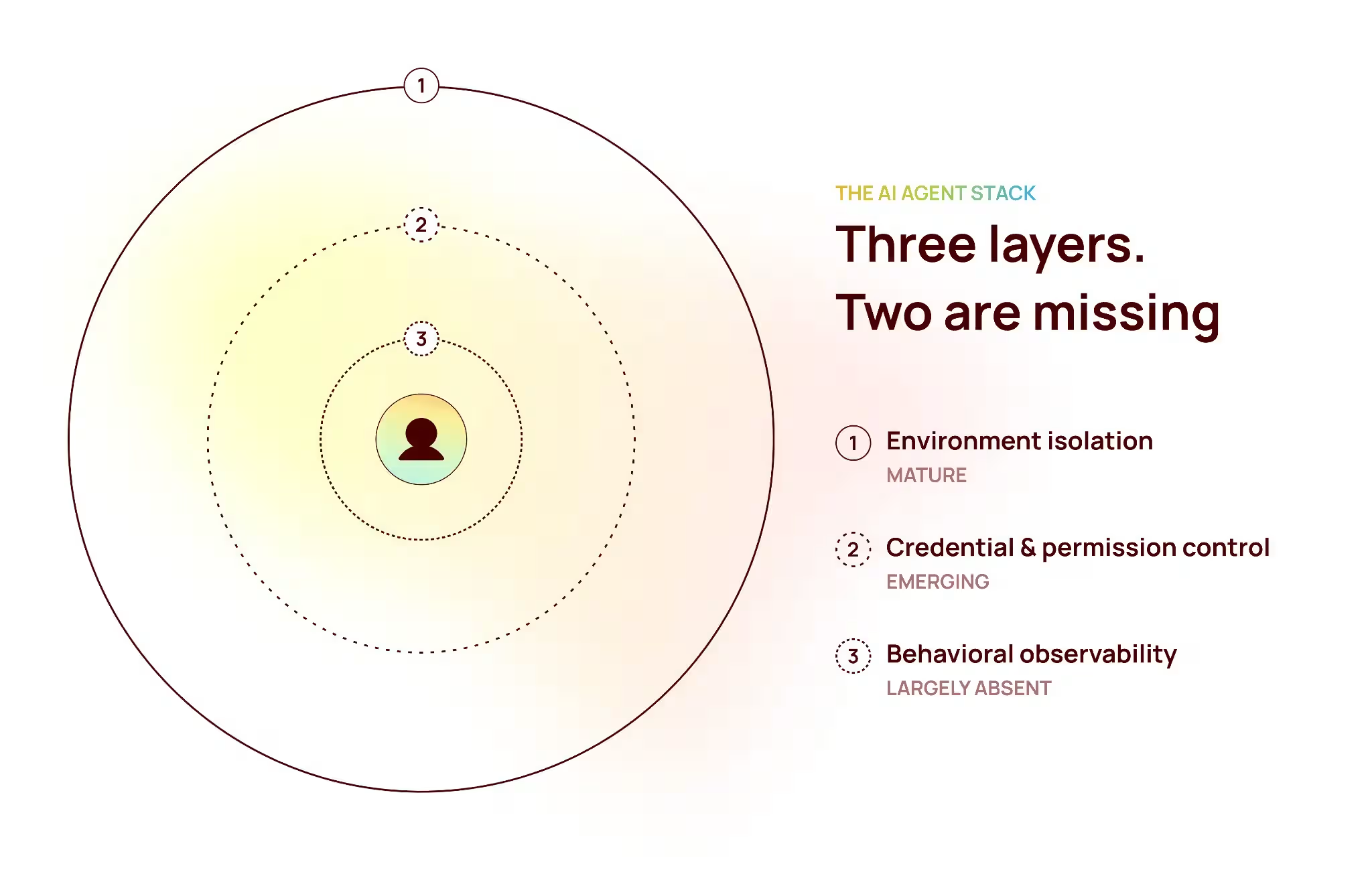
The agent stack is missing two layers and the field just figured it out
by
Kirt Debique
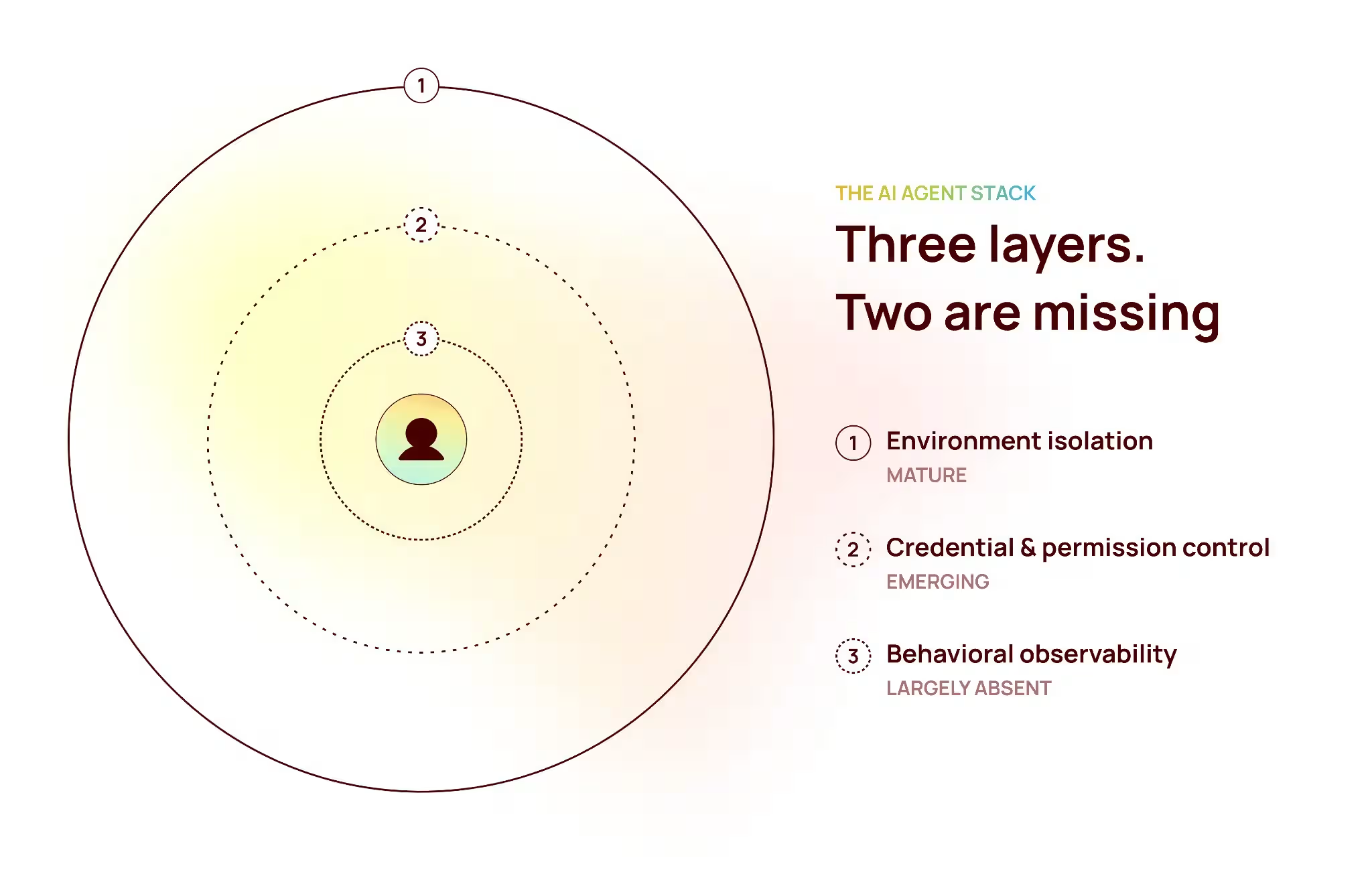
The agent stack is missing two layers and the field just figured it out
by
Kirt Debique

May 3, 2026
Why your SIEM can’t solve identity security and what it actually takes
by
Siva Garudayagari

Why your SIEM can’t solve identity security and what it actually takes
by
Siva Garudayagari

April 22, 2026
The breach didn’t break in. It walked in through a door you opened.
by
Jagadeesh Kunda

The breach didn’t break in. It walked in through a door you opened.
by
Jagadeesh Kunda

April 22, 2026
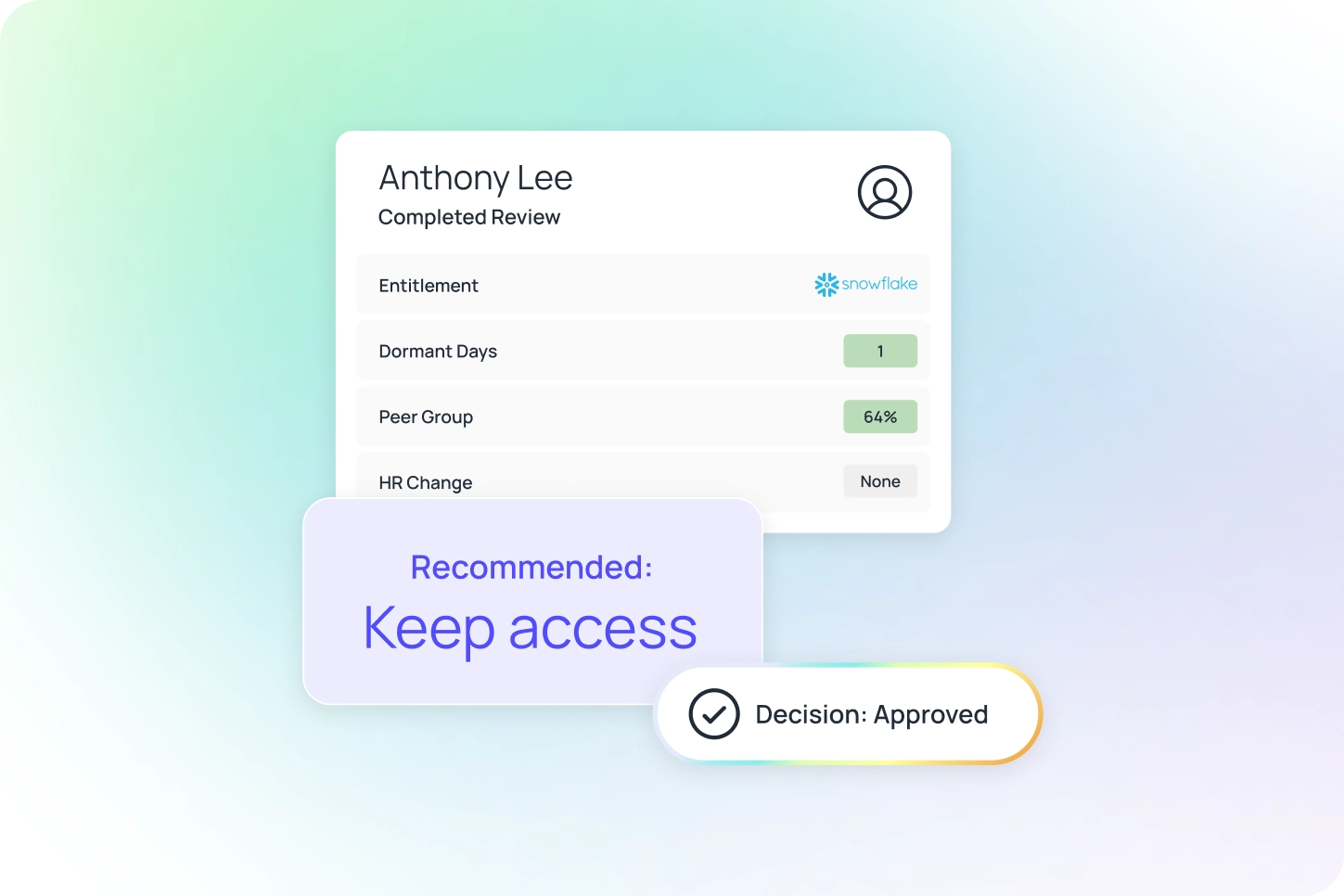
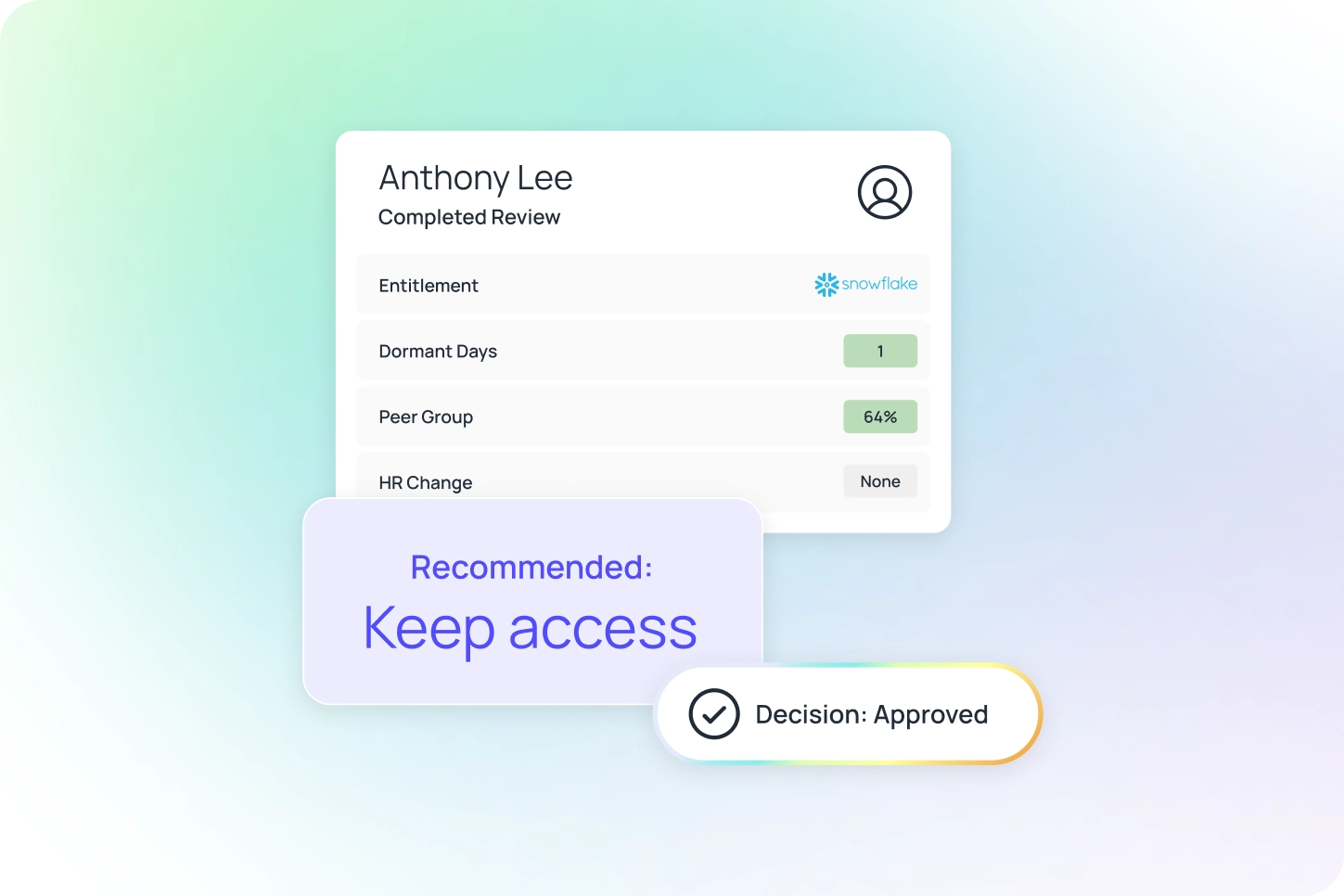
The prompt injection problem isn't solvable — but the permissions problem is
by
Jagadeesh Kunda

The prompt injection problem isn't solvable — but the permissions problem is
by
Jagadeesh Kunda

April 14, 2026
Just-in-time access: how to eliminate standing privileges and reduce risk
by
Oleria

Just-in-time access: how to eliminate standing privileges and reduce risk
by
Oleria

April 14, 2026
Segregation of Duties: A Guide to Automated SoD
by
Oleria

Segregation of Duties: A Guide to Automated SoD
by
Oleria
April 14, 2026
SOX Compliance Checklist: How identity automation helps pass audits
by
Oleria
SOX Compliance Checklist: How identity automation helps pass audits
by
Oleria

April 10, 2026
Governing AI agent identity: a practitioner's guide
by
Jagadeesh Kunda

Governing AI agent identity: a practitioner's guide
by
Jagadeesh Kunda

April 9, 2026
If you want AI to move faster, fix identity first
by
Jim Alkove

If you want AI to move faster, fix identity first
by
Jim Alkove
No results

.webp)
%20(1).png)